The project work aims
at designing a student attendance system which could effectively manage
attendance of students of the department of Computer Science and Engineering at
Jatiya Kabi Kazi Nazrul Islam University. In this project work, attendance is
marked after students biometric identification. For student identification, a
fingerprint recognition based identification system is used. Fingerprint
features are considered to be the best and fastest method for biometric
identification. These features are more secure to use and unique for every
person that dont change in ones lifetime. Fingerprint recognition is a mature
field today, but still identifying individual from a set of enrolled
fingerprints is a time taking process. It was very necessary to improve the
fingerprint identification system for implementation on large databases, e.g.
of an institute or a country. In this project, the minutiae algorithm is used
to develop the identification system which is faster in implementation than any
other available today in the market. The proposed automated attendance system
based on fingerprint recognition was tested on a class of student fingerprint
databases and achieved significant results for taking an attendance of the
students of the Department of Computer Science and Engineering. The proposed
system has been implemented using C# programming paradigm platform.
Introduction
The present is the revolutionary time of computer technology. Most of the
works depends on computer application. The
traditional student attendance includes all the hassles of roll calling and
very time consume of the students as well as teachers for conducting the
classes in the department. The process is very boring and very time-consume of
the students as well as teachers. So, a new approach will be needed to handle
this process. This motivates us to design a reliable system for student
attendance. The Biometric Identification Systems are widely used for unique identification
of humans, like students, mainly for verification and identification. Also, the
use of biometric features in student attendance management system is a secure
approach. A biometric system can be either an identification system or a
verification (authentication) system.Several biometric features are used for user verification. These are DNA
Matching (Chemical Biometric), Ear(Visual Biometric), Eyes (Iris Recognition
and Retina Recognition), Face Recognition (Visual Biometric), Fingerprint Recognition
(Visual Biometric), Gait (Behavioral Biometric), Signature Recognition (Visual/Behavioral
Biometric), Speech
and Speaker Recognition (Auditory Biometric ),
etc. Designing and developing a student
attendance system based on fingerprint recognition manages records for
attendance in the departments like CSE department of Jatiya Kabi Kazi Nazrul
Islam University will be hassles-free, accurate and save valuable time of
students as well as teachers for conducting the classes.
Automated Attendance Systems
An automated system eliminates the need
for paper tracking and instead makes use of barcode badges, electronic tags,
touch screens, magnetic stripe cards or even biometrics (fingerprints, retinal
scans and facial features). This makes life easier for both the employee and
the business as work hours are logged automatically when the employee enters
and leaves the office. This eliminates the possibility of timesheets getting
lost or manipulated. It also saves a lot of time for the payroll department
since automated systems usually have integrated reporting functionalities which
take care of most of the pay processing. Several types of automated attendance
systems are available, such as, Radio Frequency Identification Cards Based
Attendance System [1], Barcode Attendance Tracking System [2], Smart Card
Access Control Attendance Systems [3], Punch Card Based Attendance System [4], Magnetic Stripe Card Based
Attendance Systems [5], Biometric Attendance System [6], etc. Biometric time
and attendance system has brought more precise system to measure group or
individuals activities and attendance as well. This includes the addition of
the different options; such as, Fingerprint Based Attendance System [7], Retina
Based Attendance System [8] and Face Recognition Attendance Systems [9]. In
this project work, fingerprint-based attendance system has been introduced for
automatically monitoring and calculating the student attendances in a class.
Fingerprint
Recognition
Fingerprints are considered to be the best and fastest
method for biometric identification. They are secure to use, unique for every
person and do not change in ones life time. A fingerprint recognition system
operates either in verification mode or in identification mode [10]. Automated
fingerprint identification is the process of automatically matching one
or many unknown fingerprints against a database of known and unknown prints. Automated fingerprint verification is
a closely related technique used in applications such as attendance and access
control systems. On a technical level, verification systems verify a claimed
identity (a user might claim to be John by presenting his PIN or ID card and
verify his identity using his fingerprint), whereas identification systems
determine identity based solely on fingerprints.
The
matching algorithm plays a key role in a fingerprint recognition system.
Matching algorithms are used to compare previously stored templates of
fingerprints against candidate fingerprints for authentication purposes [11].
Two majorly used algorithms are Pattern-based
(or image-based) algorithms and Minutia Feature extraction based algorithms [12]. Pattern based algorithms compare the
basic fingerprint patterns (arch, whorl, and loop) between a previously stored
template and a candidate fingerprint. Other algorithms use minutiae features on
the finger. The major Minutia features are ridge ending, bifurcation, and short
ridge (or dot) [13]. The ridge ending is the point at which a ridge terminates.
Bifurcations are points at which a single ridge splits into two ridges. Short
ridges (or dots) are ridges which are significantly shorter than the average
ridge length on the fingerprint. Minutiae and patterns are very important in
the analysis of fingerprints since no two fingers have been shown to be
identical. The Minutia Feature extraction based algorithm has been used for
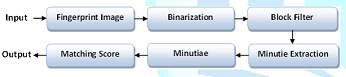
matching the fingerprint templates in this project work. The algorithmic steps
of the Minutia Feature extraction based
algorithm is shown in Figure-1 [14].
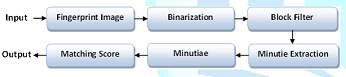
Figure 1: Implementation of Minutia Feature Extraction Based Algorithm.
Binarization
converts gray scale image into binary image by fixing the threshold value. The
pixel values above and below the threshold are set to 1 and 0 respectively. Its
the most critical task in the fingerprint matching system. The binarized image
is thinned using Block Filter to reduce the thickness of all ridge lines to a
single pixel width to extract minutiae points effectively. Thinning preserves
outermost pixels by placing white pixels at the boundary of the image, as a
result first five and last five rows, first five and last five columns are
assigned value of one. The minutiae location and
the minutiae angles are derived after minutiae extraction. The terminations
which lie at the outer boundaries are not considered as minutiae points, and
Crossing Number isused to locate the minutiae points in fingerprint image.
Crossing Number is defined as half of the sum of differences between intensity
values of two adjacent pixels. If crossing Number is 1, 2 and 3 or greater than
3 then minutiae points are classified as Termination, Normal ridge and
Bifurcation respectively. To compare the input fingerprint data with the
template data Minutiae matching is used. For efficient matching process, the
extracted data is stored in the matrix format.
During
the matching process, each input minutiae point is compared with template
minutiae point. In each case, template and input minutiae are
selected as reference points for their respective data sets. The reference
points are used to convert the remaining data points to polar coordinates. Matching an input image with a stored template
involves computing the differences using distance measures techniques [15]. The matching score is combined with that obtained
from the minutiae-based method, using the some rule of combination [16]. If the
matching score is less than a predefined threshold, the input image is said to
have successfully matched with the template.
Methodological Steps
The
methodological steps of the system are pictures by the block diagrams and shown
in Figure-2. The proposed system has the following five major components.
a)
User
and Device Interface
b)
Data
Acquisition with Fingerprints
c)
Fingerprint
Processing
d)
Fingerprint
Verification
e)
Attendance Report Generation
User
Interface is the communication between a user and the system. In the proposed
system there are three panels, as shown in Figure-3. One is for the admin, one
is for the teacher and the last one is for the student. Admin have to login the
system in two ways. One is by providing the admins fingerprint and another way
is to provide the username and password.
To view Figure 3, click below
Figure 3: System User Interface.
To view Figure 4, click below
Figure 4: Block Diagram of Admin Panel.
Admin
can add a students information, can add course, can assign courses to the
teacher, can see the student and teacher report and can view the all students
information at any time. The user interface also includes two registration
forms that is used to get student and teacher information and their
fingerprint. All the information about the student and teacher are taken
through these form. In
teacher panel, every teacher gets a profile after registration. This profile
shows all the basic information about the teacher. Admin assign different
courses to different teacher. When a course is assigned to a teacher then it
appears in his/her profile. Then the teacher can take attendance to each class
both by manually or through fingerprint.
In
student panel, student can only verify themselves through their fingerprint.
When a student enrolls his finger the device collects his fingerprint template
and matches this template with the entire stored template. If the template
matches with any template then he/she is a verified student, otherwise not.
The
system made the successful connection of fingerprint device with the computer,
referred as fingerprint device interface. The device can be connected with the
computer through 3 ways, such as TCT/IP Communication, Serial Port
Communication and USB Client Communication. Here the fingerprint device was
connected with the PC by using TCP/IP communication port.
The
system received the students Information by filled in the registration form and
the students fingerprints from the fingerprint scanner as input, as shown in Figure-5. The fingerprint scanner can read
fingerprints of any or more fingers of the both hands. The basic information
was stored in the student profile table and the fingerprints were in the
template data table. In this template table the key field is the student roll
number. By this roll number all the templates are differed from one another.
To view Figure 5, click below
Figure 5: Student Registration with Fingerprints.
Fingerprint Processing
When
a student enrolls his finger on the devices scanner sensor, the device scans
the edge and ridge of the finger. Then it set some value from the position of
that ridges and edges and combines them. Finally from this point of fingers
ridge and edge the device create binary template that is known as fingerprint
template. The proposed system used these templates in the further steps, such
as identification and verification.
Fingerprint Identification and Verification
Student
Identification should be done by students fingerprint. For identification, the
device scans the ridge and edge of the finger and creates a template. The
system searches all the templates that are stored in the system database and
matches with each saved template. If the templates match with the existing
template then all the information of identified student have been displayed in
the dash board, as shown in Figure-6. But if the template is not matched with
any existing template then the system notifies that the user is not the valid
student of the department. The teacher can take the
student attendances through the fingerprint of the student by using fingerprint
verification process.
To view Figure 6, click below
Figure 6: Student Identification Form using Fingerprint.
Taking Class Attendance
The teacher can
login the system by his/her username password or by fingerprint. The assigned
courses are appeared in his/her profile, as shown in Figure-7. Then the teacher can take
attendance to each class both by manually or through fingerprint. Teacher can take attendance
through the fingerprint of the student. The process was done by fingerprint
verification. The verified students attendances were stored in the attendance
database. They can also take attendance manually by clicking the checkbox from
the list of students, as shown in Figure-8.
To view Figure 7, click below
Figure 7: Teacher Profile Form.
To view Figure 8, click below
Figure 8: Taking Student Attendance Form.
To view Figure 9, click below
Figure 9: Details Attendance Report.
Attendance Report Generation
Finally, the student attendance report was generated from the
attendance table. Two types of reports are available here. One is details
report that contains the date by date attendance, total attended, total absent,
percentage and the marks, as shown in Figure-9. The
short report does not contain the date by date attendance.
An applicable attendance management system was
designed for educational organizations in this project. This project mainly
comprised of development of attendance management system and fingerprint
identification system. This project presented a framework in which attendance
management was made automated and on-line. There are some limitations of the
fingerprint technology. These are the inability to enroll some users for poor
fingerprints. For these cases one need to consider another biometric features.
Also it can suffer some small changes along the time. To overcome this problem,
the system may be necessary to re-enroll the fingerprint and/or use multiple
fingerprints enrollment. The system needs to deploy specialized devices for
fingerprint enrollment. In future this project can be extended to store fingerprint databases on the remote server that can be used over
world-wide. A website will be hosted on the server for online access to
attendance reports. The proposed system has been developed using C# programming
paradigm platform. The proposed system can be implemented for all classes of
the university if sufficient funds will be provided to us.
References
1.
Lim
TS, Sim SC and Mansor MM. RFID based attendance system. 2009 IEEE Symposium on
Industrial Electronics & Applications (2009) Kuala Lumpur 778-782. https://doi.org/10.1109/ISIEA.2009.5356360
2.
Yakub
Saheed, Hambali Moshood, A Adedeji, Abdulmumeen and A Adeniji, I. Attendance
Management System Using Barcode Identification on Students Identity Cards
(2016) Pacific J Sci Technol 17: 224-230.
3.
Using
smart card for secure physical access. A smart card alliance report, Smart card
alliance Inc (2003) Princeton Junction, NZ.
4.
Yasmin
Khan. Punch Card Attendance Monitoring System (2010) MS Thesis, Dept. of
Computer Science and Infromation Technilogy, Jinnah University for Women,
Bangladesh.
5.
Daniel
Ramsbrock, Stepan Moskovchenko and Christopher Conroy. Magnetic Swipe Card
System Security A case study of the University of Maryland, College Park.
6.
A
Ujan and Ismaili IA. Biometric attendance system (2011) The 2011 IEEE/ICME
International Conference on Complex Medical Engineering, Harbin Heilongjiang,
499-501.
7.
Akinduyite
CO, Adetunmbi AO, Olabode OO and Ibidunmoye EO. Fingerprint-Based Attendance
Management System (2013) J Computer Sci Applications 5: 100-105. DOI:
10.12691/jcsa-1-5-4
8.
Khatun
AK, Haque MF, Ahmed S and Rahman MM. Design and implementation of iris
recognition based attendance management system (2015) International Conference
on Electrical Engineering and Information Communication Technology (ICEEICT),
Dhaka.
9.
Chintalapati
S and Raghunadh MV. Automated attendance management system based on face
recognition algorithms (2013) IEEE International Conference on Computational
Intelligence and Computing Research, Enathi.
10. Salil
Prabhakar, Sharath Pankanti, Anil K Jain. Biometric Recognition: Security and
Privacy Concerns (2003) IEEE Security and Privacy Magazine.
11.
Kumar
DA and Ummal Sariba Begum. A Comparative Study on Fingerprint Matching Algorithms
for EVM (2013) J Computer Sci Applications 55-60. DOI: 10.12691/jcsa-1-4-1
12.
Sangeeta
Narwal and Daljit Kaur. Comparison between Minutiae Based and Pattern Based
Algorithm of Fingerprint Image (2016) I.J. Information Engineering and
Electronic Business 2: 23-29. http://dx.doi.org/10.5815/ijieeb.2016.02.03
13.
Yager
N and Amin A. Fingerprint verification based on minutiae features: a review
(2004) Pattern Analysis and Applications 7: 94-113. https://doi.org/10.1007/s10044-003-0201-2
14.
Md.
Mijanur Rahman, Sifat Nur Rahman, Mahbubur Rahman and Firoz Haider. Biometric
Student Registration and Verification System (2016) Discovery 52: 2399-2407.
15.
Roberto
Brunelli. Template Matching Techniques in Computer Vision: Theory and Practice.
Wiley Publication, USA.
Jain AK, Prabhakar S,
Hong L and Pankanti S. Filterbank-based fingerprint matching (2000) IEEE Trans
Image Process 9: 846-859. https://doi.org/10.1109/83.841531
*Corresponding
author:
Md. Mijanur Rahman, Associate Professor, Department
of Computer Science and Engineering, Jatiya Kabi Kazi Nazrul Islam University,
Bangladesh, Tel: +8801712594569, E-Mail: mijanjkkniu@gmail.com
Citation:
Rahman S, Rahman M, Rahman MM. Automated Student Attendance System using
Fingerprint Recognition (2018) Edelweiss Appli Sci Tech 2: 90-94
Attendance
System; Biometric Features; Fingerprint Recognition; Identification;
Verification.